summary
Help page on how to perform SSO with SAML authentication at TROCCO.
About SSO
Single Sign On (SSO) is a mechanism that allows users to log in to multiple web services and applications with a single authentication using a single set of IDs and passwords.
SSO with SAML authentication is available only for subscribed accounts on the Essential plan and above.
Advantages of Implementing SSO
The following advantages are possible
- Convenience is improved because only one set of IDs and passwords need to be recorded.
- Eliminates the need to manage passwords for as many services as you use.
- The ability to manage all available services for each employee in one place reduces the burden on the administrator.
About SAML Authentication
TROCCO uses the Security Assertion Markup Language (SAML) method as its SSO authentication method.
In the SAML system, the party providing authentication information is defined as the Identity Provider (IdP), and the party using the authentication information is defined as the Service Provider ( SP).
In the following, we will describe the steps for setting up each of these separately for IdPs (Okta, Entra ID, Onelogin, GMO Trust Login, etc.) and for SPs (TROCCO).
TROCCO uses IdP Initiated SSO as its SSO login flow.
When logging into TROCCO using SSO, please log in from the IdP (Okta, Entra ID, Onelogin, GMO Trust Login, etc.) side.
For details on how to set up the IdP side of GMO Trust Login, please refer to TROCCO's How to Set Up SAML Authentication.
Setup procedure
advance preparation
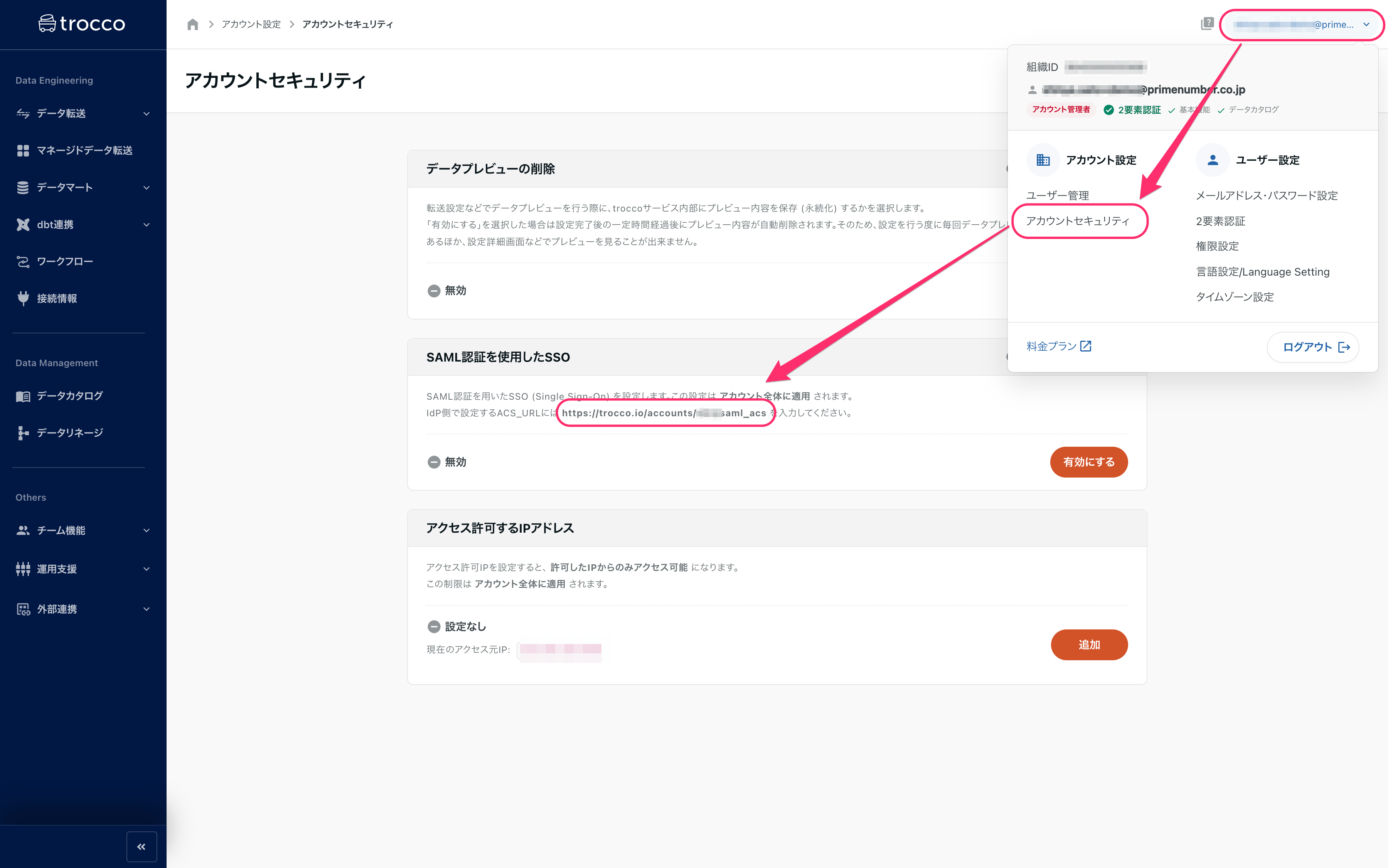
The Assertion Consumer Service URL ( ACS_URL) specified by TROCCO is required when configuring the IdP side.
The ACS_URL is different for each TROCCO account.
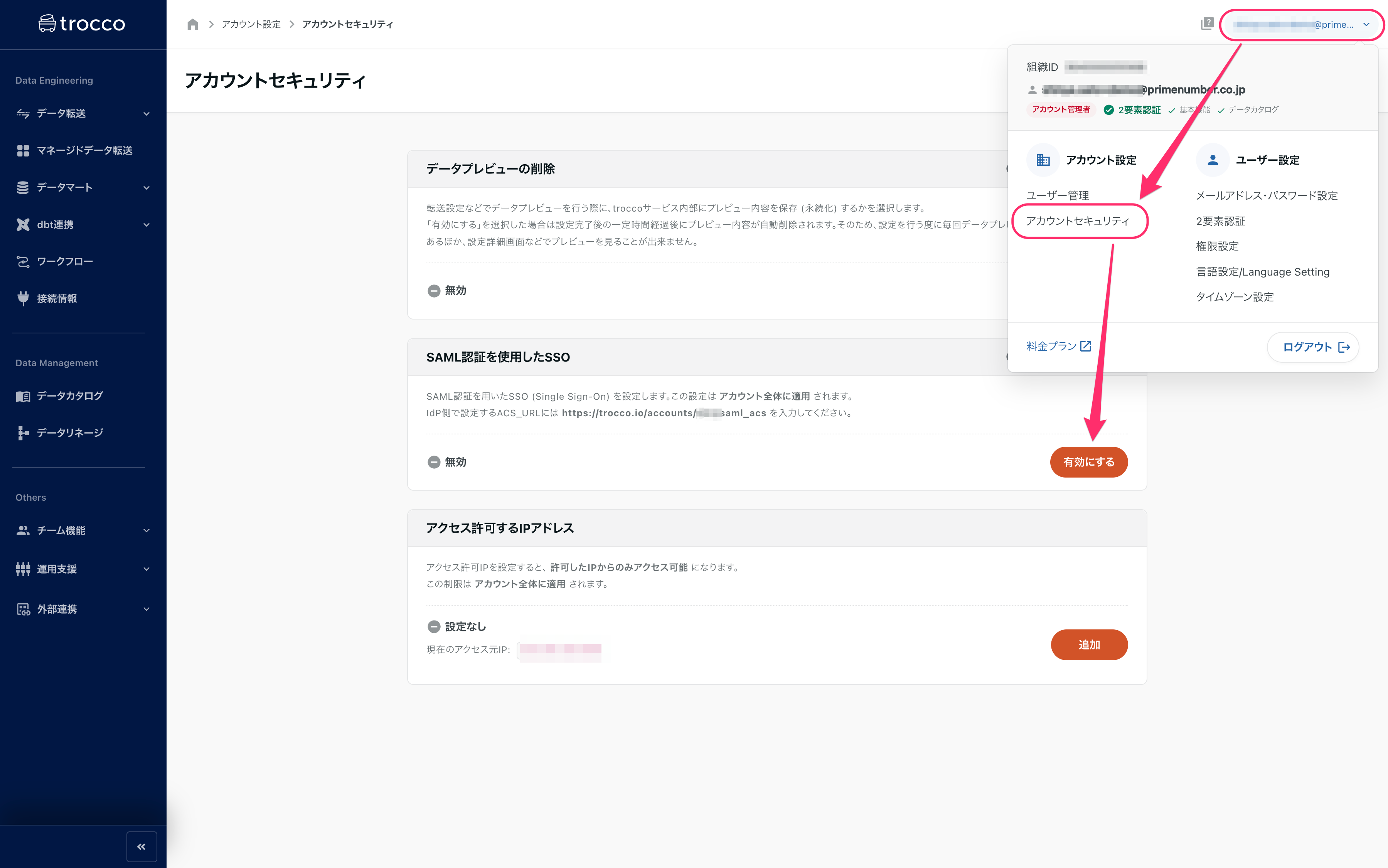
Click on the email address section in the upper right corner of the TROCCO screen > Account Security, and check the URL under SSO using SAML authentication.
When registering TROCCO with IdP, you may be required to upload an application logo.
The TROCCO logo can be downloaded from our website.
IdP-side settings
The following three major settings are used.
- Register TROCCO as SP in IdP.
- Assign users and groups to registered SPs (TROCCO)
- Obtaining IdP metadata
Information required to register TROCCO with IdP
Below is the information required to register TROCCO as an SP with the IdP.
- Assertion Consumer Service URL(ACS_URL)
- Specify the ACS_URL obtained in the advance preparation.
- SP Entity ID
https://trocco.ioを指定します.
- NameID Format
- Specify the
Email(orEmailAddress).
- Specify the
Some IdPs may use a different name for the input field name. The following are typical examples
- ACS_URL:Single sign on URL
- SP Entity ID:Audience URI
Below is a description of the setup procedure, using Okta as an example.
STEP1 Register TROCCO as an SP
-
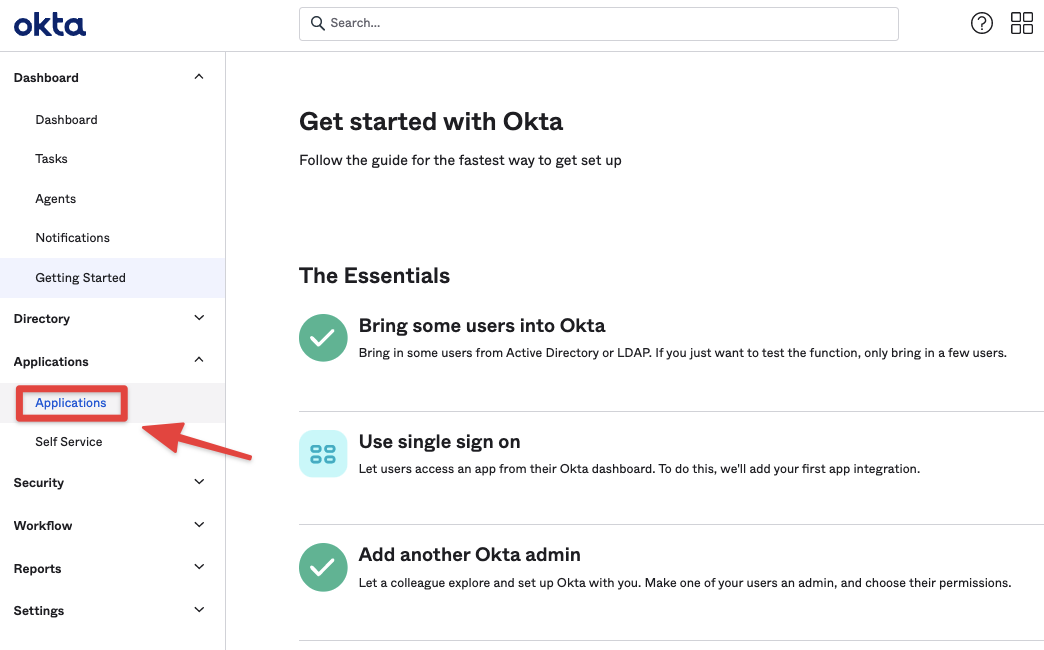
From the menu of the Okta administration page, click on Applications>Applications.
-
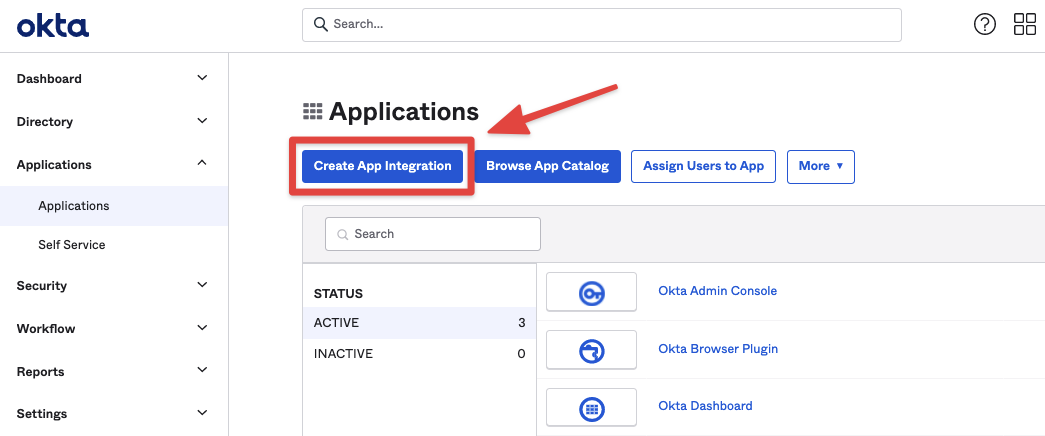
Click Create App Integration.
-
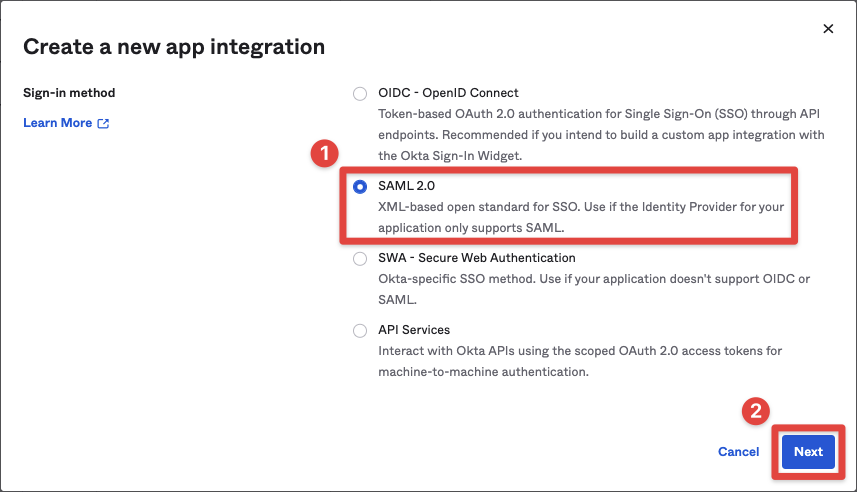
Select SAML 2.0 and click Next.
-
Configure as appropriate in General Settings and click Next.
- Enter
troccoin the App Name field.
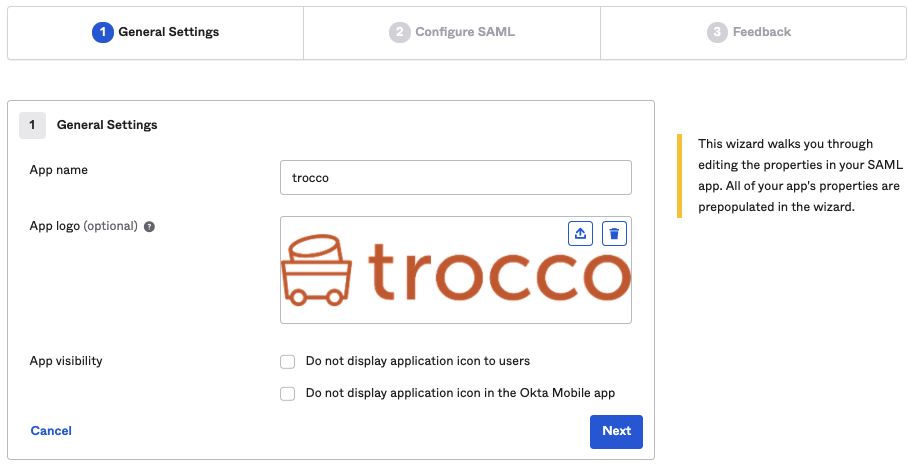
- Enter
-
Configure SAML accordingly and click Next.
- Refer to the information required when registering TROCCO with IdP and specify each setting value.
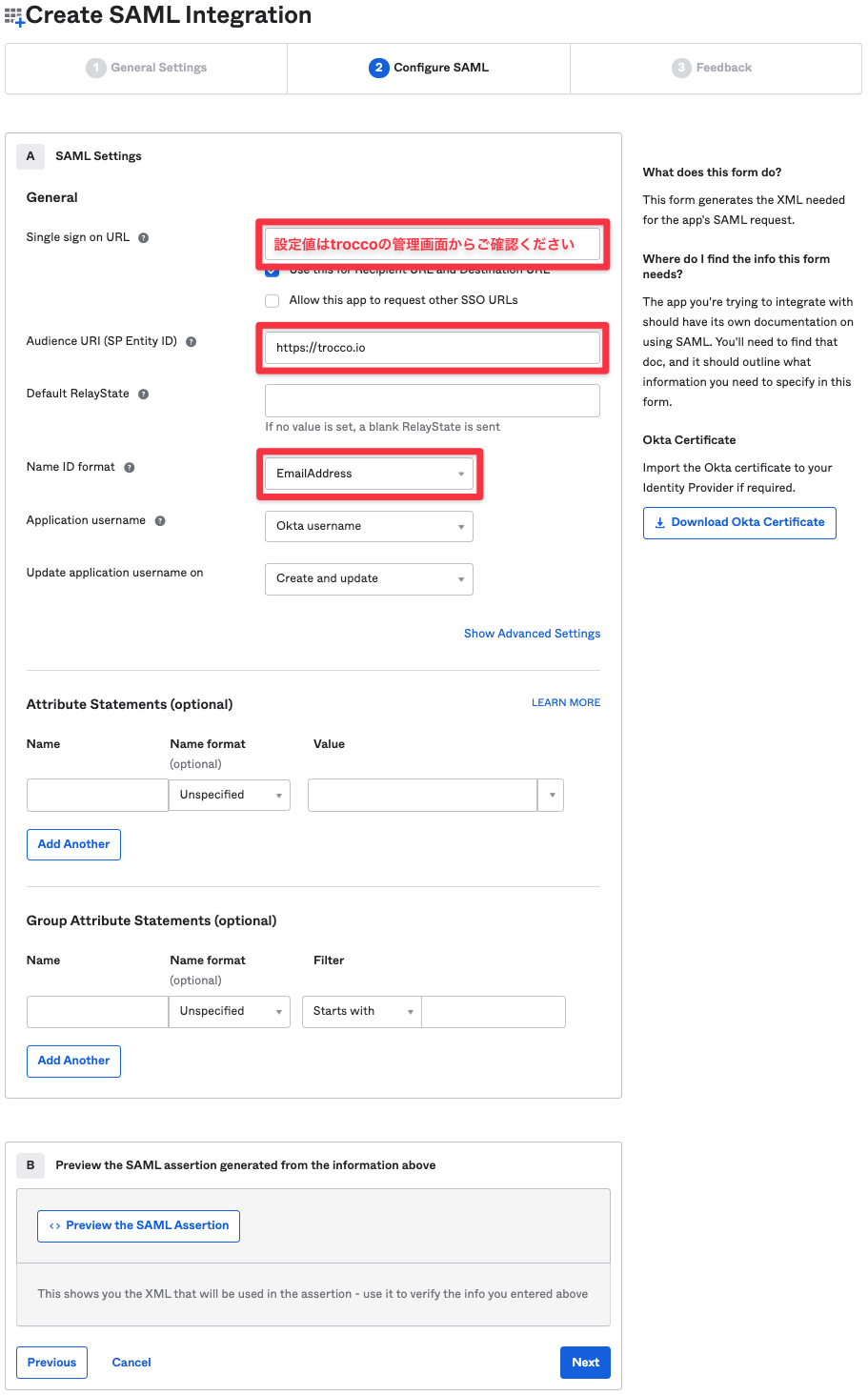
- Refer to the information required when registering TROCCO with IdP and specify each setting value.
-
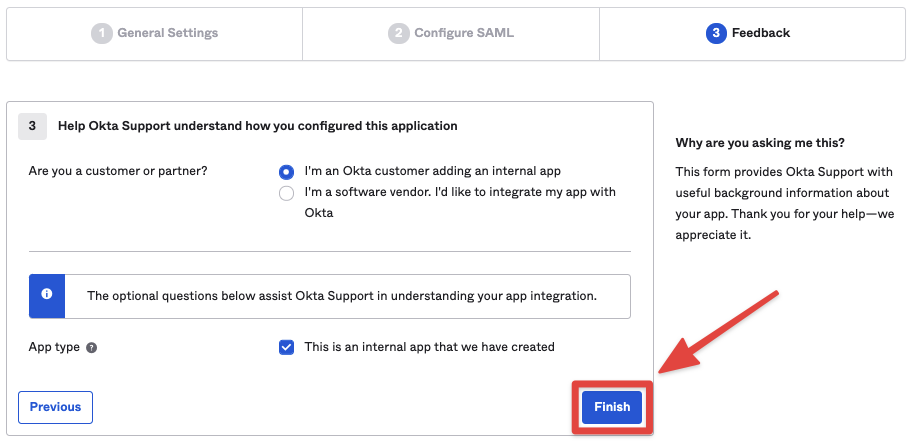
Respond to Feedback as appropriate and click Finish.
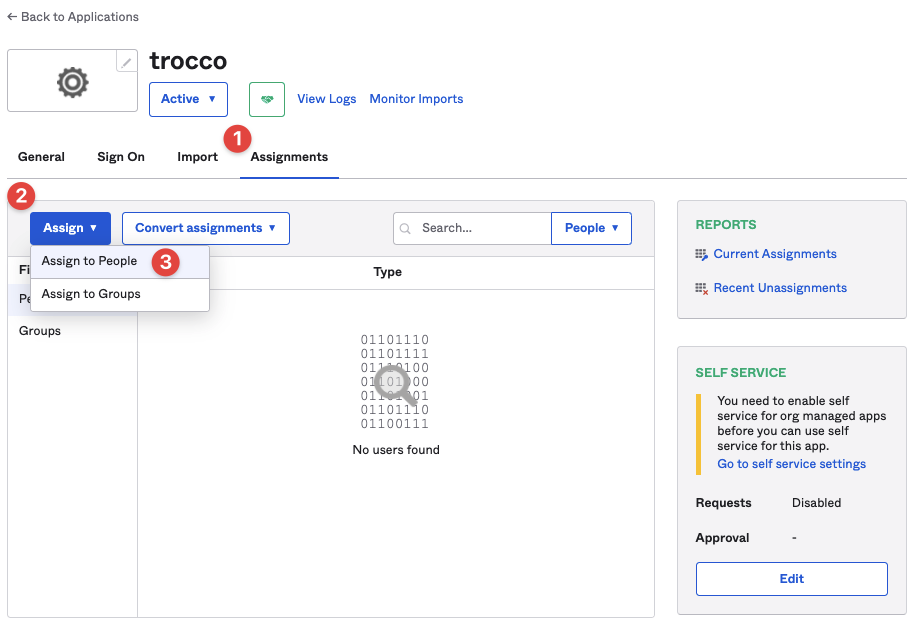
STEP2 Assign users and groups
Click Assignments > Assign, then Assign to People or Assign to Groups as appropriate.
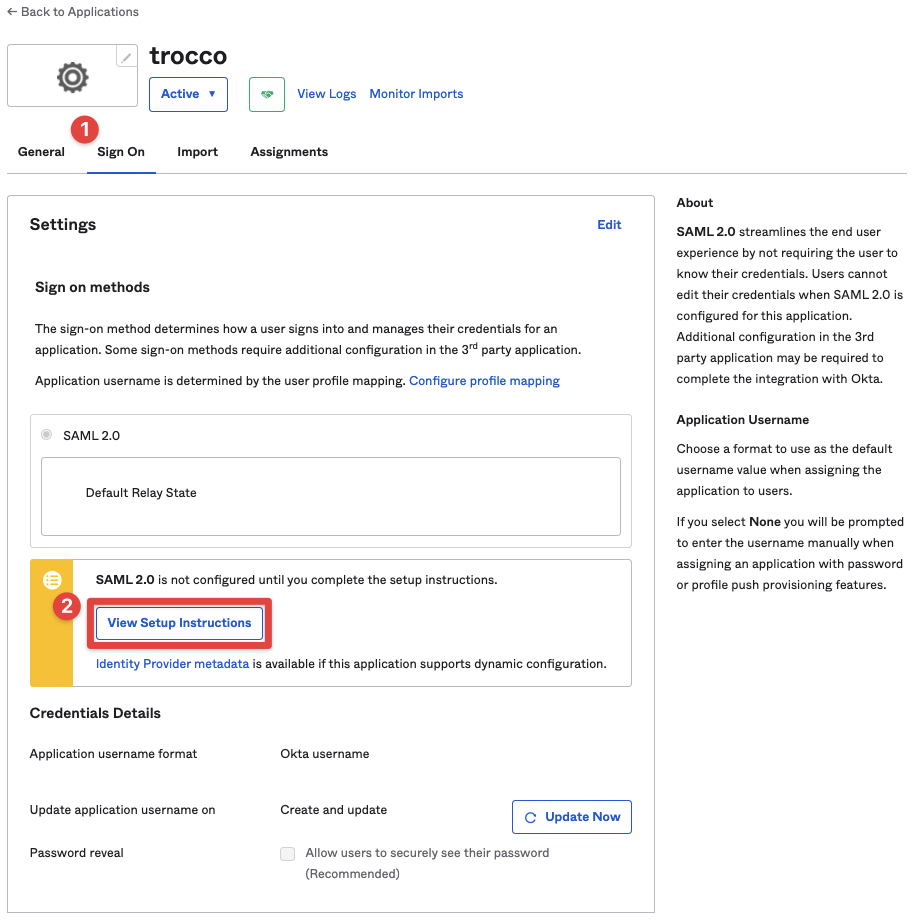
STEP3 Obtain IdP metadata
-
Click Sign On > View****Setup Instructions.
-
Click on Optional at the bottom of the screen that appears.
Provide the following IDP metadata to your SP provider will be displayed.
Record the metadata displayed.
If you are using Entra ID (formerly Azure AD), you do not need to set the sign-on URL, relay state, or log-out URL.
Set the identifier and response URL.
- identifier
https://trocco.io/を指定します.
- response URL
- Specify the ACS_URL obtained in the advance preparation.
Settings on the TROCCO (SP) side
Register IdP metadata with TROCCO.
-
Click on the email address section in the upper right corner of the TROCCO screen > Account Security, then click on Enable****from SSO using SAML authentication.
-
Enter the values obtained in STEP3 Obtaining IdP metadata and click Save.

If you disable password authentication as a method of logging into TROCCO and use SSO only, please enable the Require login with SAML authentication option.
You can invite users as you did before setting up SAML authentication.
In doing so, however, be sure to match the email address of the user assigned by the IdP with the email address to be added to TROCCO.